The modern workforce is no longer bound by office walls. The demand for flexibility has made “Bring Your Own Device” (BYOD) a critical topic in every IT department. While the promise of increased productivity and employee satisfaction is alluring , the potential for security chaos and unforeseen costs is a serious concern.
A successful BYOD program is not a simple switch you flip; it’s a strategic initiative that requires careful planning, robust technology, and a deep understanding of your organization’s culture and risks. This guide provides a strategic framework to help you move from the potential chaos of unmanaged devices to the controlled, secure, and productive environment you need.
The strategic evaluation: is BYOD right for your organization?
Before implementation, a clear-eyed assessment is fundamental. BYOD is not a universal solution, and its success depends on your specific context.
- Your corporate culture
BYOD thrives in companies that value flexibility, autonomy, and trust in their employees. If your organization is more hierarchical, implementing BYOD could require a significant cultural shift and a review of internal policies.
- Your data sensitivity
The type of data your employees access is a key factor. If your company handles highly confidential information, such as financial or medical data, you will need additional security measures to ensure compliance. For low-risk data, BYOD can be a simpler path.
- Your workforce needs
The model is particularly valuable for a mobile workforce. Employees who work remotely or travel frequently gain greater flexibility, which can lead to higher satisfaction and productivity. This makes it a strong choice for departments like Sales, Marketing, and consulting roles that depend on mobility.
- Your resources and budget
While BYOD can seem cheaper on the surface, it introduces new costs. Be prepared for investments in a Mobile Device Management (MDM) solution like Applivery, employee training, and dedicated technical support for a wide variety of devices.

The pillars of successful BYOD implementation
Once you’ve decided to proceed, success rests on three core pillars. Neglecting any one of them can undermine the entire program. A truly successful BYOD initiative is not just a technology project; it’s a comprehensive business strategy that balances rules, tools, and people. These three pillars—a robust policy framework, a secure technology stack, and a human-centric communication plan—are deeply interconnected. To build a program that lasts and delivers a true strategic advantage, you must develop all three in tandem.

A rock-solid policy framework
A clear and concise BYOD policy is the foundation of your program. It must be established before any devices are enrolled and should explicitly define:
- Approved devices and requirements: specify the types of smartphones, tablets, and laptops permitted, along with minimum hardware and operating system versions. It’s recommended to require the latest OS version unless a specific incompatibility exists.
- Access controls: define which company resources, such as email, business applications, and the intranet, are accessible from personal devices.
- Security mandates: establish the non-negotiable security measures that will be implemented, including the use of secure passwords, multi-factor authentication, and data encryption.
- Employee responsibilities: clearly outline the employee’s role in protecting confidential company information and adhering to all security policies.
A robust technology stack
A strong policy is ineffective without the technology to enforce it. The biggest technical challenge of BYOD is managing a diverse ecosystem of devices and operating systems. This is where a unified and intuitive UEM platform becomes the cornerstone of your strategy.
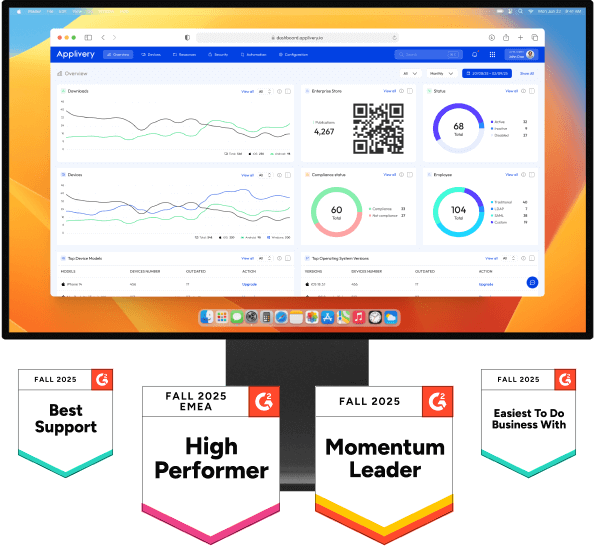
For instance, Applivery is built to provide a single pane of glass for managing both Apple and Android devices, simplifying the complexity that a diverse BYOD environment creates. Your technology stack must include:
-
Mobile Device Management (MDM): an MDM solution is fundamental to any BYOD strategy. It allows you to control access to company data, apply security policies, and remotely wipe corporate information if a device is lost or stolen.
-
Multi-Factor Authentication (MFA): enhance security with strong passwords and MFA to add a critical layer of protection. MFA requires users to provide two or more verification factors, making it significantly harder for unauthorized users to gain access.
-
Data encryption: protect sensitive information by ensuring it is encrypted, both when stored on the device and when it is being transmitted.
A human-centric approach
The most common point of failure is not technology, but people. Building trust and ensuring clarity is paramount.
-
Clear communication: it is crucial to explain the benefits of the BYOD program and what is expected of employees. Address privacy concerns head-on by being transparent about what the company can and cannot see on their devices.
-
Facilitate adaptation: provide your team with the resources they need to succeed, such as tutorials, user guides, and dedicated technical support.
-
Build a culture of trust: a successful BYOD program relies on a culture of mutual trust and responsibility. Make it clear that you trust your team to use their devices responsibly and adhere to the security policies you’ve put in place.
Finding the right fit: choosing your device model
A one-size-fits-all approach rarely works. The most effective strategies often combine different models based on departmental needs. Here’s how to choose the right fit for your departments:
-
BYOD is ideal for: Sales and Marketing teams that require high mobility and flexibility to work from anywhere.
-
CYOD (Choose Your Own Device) is ideal for: IT, Software Development, and Finance departments that handle sensitive information or require powerful, standardized hardware. In this model, the company provides employees with a limited selection of devices from which they can choose.
-
COPE (Corporate-Owned, Personally Enabled) is ideal for: Senior management and other roles that need a balance of high security and personal flexibility. In this approach, the company provides the device and maintains control, but allows for some personal use.
The challenge, then, becomes managing this diverse and hybrid environment without creating exponential work for your IT team. A flexible Unified Endpoint Management (UEM) platform that can handle these various enrollment types from a single console is critical to making this strategy work. For instance, Applivery is designed to manage BYOD, CYOD, and COPE models from one intuitive dashboard, giving you the power to choose the right model for each team and the unified control to manage them all efficiently.
The path to a strategic advantage
Implementing a BYOD program is a significant undertaking, but it doesn’t have to be a high-risk gamble. By conducting a strategic evaluation, building your program on the three pillars of policy, technology, and communication, and choosing the right models for your teams, you can create a secure, productive, and flexible work environment. This dedication to driving both performance and security is at the core of Applivery’s mission: to empower you to build a flexible, high-achieving workforce on a foundation of unshakeable security.
This guide provides the strategic framework. To explore every detail, from eligibility checklists to in-depth cost analyses and implementation roadmaps, you can find out more in our complete BYOD in the Enterprise whitepaper.
Frequently asked questions (FAQ)
What is the main difference between BYOD and CYOD?
The primary difference comes down to ownership and control. In a BYOD model, the device is the employee's personal property, and they have full control over it. In a CYOD (Choose Your Own Device) model, the company owns the device and retains control over it through IT policies, even though the employee gets to choose their preferred device from a limited, company-approved list.
Is implementing a BYOD policy always cheaper for the company?
Not necessarily. While BYOD is often perceived as a way to reduce expenses on hardware, in many cases it does not generate the expected savings. This is due to additional or "hidden" costs related to technical support for a variety of devices, security management tools like MDM, and employee training.
Will the company be able to see my personal data on a BYOD device?
No. A properly implemented BYOD program should ensure that the company does not access personal information on employee devices. A clear policy must be in place to assure employees that their privacy will be respected and that personal data will not be accessed without their consent. This is typically managed by using an MDM to create a secure, separate container for work apps and data, isolating it from personal content.
What happens if an employee loses their personal device used for work?
With a Mobile Device Management (MDM) solution in place, the company has the ability to remotely wipe corporate data in the event the device is lost or stolen. This protects sensitive company information while ideally leaving personal data untouched, especially when a containerized work profile is used.